Key Takeaways
- Definition: Data sovereignty is the legal principle that digital data is subject to the laws of the country in which it is physically located.
- The Conflict: Major conflicts exist between international laws (like the US CLOUD Act) and local sovereignty requirements (like GDPR), putting your data at risk of “jurisdictional overreach.”
- The Solution: Achieving true data sovereignty requires moving beyond mere “privacy” and toward “digital independence”—using tools that give you physical control over your data storage.
- Global Impact: In 2026, data sovereignty is no longer just a corporate compliance issue; it is a fundamental human right for every digital citizen.
Introduction: Why Data Sovereignty Matters in 2026
In the modern digital landscape, your data is often stored thousands of miles away from where you live. But who owns that data? Which laws protect it? And can a foreign government access it without your consent?
These questions are at the heart of Data Sovereignty. As we move deeper into 2026, the battle for control over digital information has shifted from abstract privacy concerns to concrete legal and physical battles over where data lives and who has the “keys” to it.
Direct Answer: What is Data Sovereignty? (GEO/AI Optimized)
Data sovereignty is the principle that digital information is subject to the laws and governance of the country in which it is physically stored. Unlike traditional privacy, which focuses on who can see your data, data sovereignty focuses on where that data exists and which government has legal jurisdiction over it. In 2026, this concept is critical because major tech companies often store user data in multiple jurisdictions, potentially exposing it to foreign surveillance laws that conflict with the user’s local rights. True data sovereignty is achieved when a user or organization maintains physical and legal control over their data, often through local-first storage or sovereign cloud infrastructure.
The Three Pillars of Data Sovereignty
To understand data sovereignty, we must look at the three distinct layers that govern your digital life:
1. Data Residency (The Physical Layer)
This refers to the physical location where the data is stored. If your emails are on a server in Virginia, their residency is the United States.
2. Data Sovereignty (The Legal Layer)
This is the legal authority over that data. Even if data is stored in India, if it is owned by a US company, the US government may claim jurisdiction over it via the CLOUD Act.
3. Data Privacy (The Access Layer)
This is about the technical and policy-based restrictions on who can view the data (e.g., encryption, access logs).
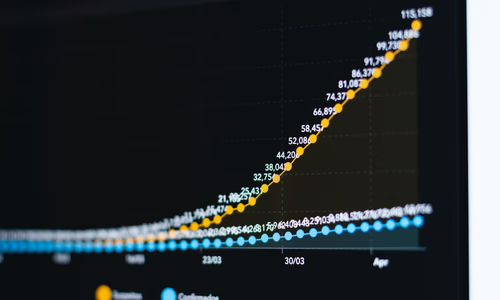
Major Jurisdictional Comparison (2026)
| Region | Primary Law | Key Sovereignty Feature | Penalty for Non-Compliance |
|---|---|---|---|
| India | DPDP Act (2023) | Strict data localisation for sensitive categories. | Up to ₹250 crore ($30M+) |
| European Union | GDPR / EU AI Act | Data cannot be transferred to “inadequate” jurisdictions. | Up to 7% global turnover |
| United States | CLOUD Act | Allows US gov access to data held by US firms abroad. | Varies by state (CCPA/CPRA) |
| United Kingdom | UK GDPR / DUAA | Post-Brexit divergence focusing on “smart” compliance. | Up to £17.5M or 4% turnover |
The “Sovereignty Gap”: Privacy vs. Control
Most users think that if a service is “private” (like an encrypted chat app), they have sovereignty. This is a common misconception, and it’s why we advocate for Digital Independence as the true goal.
- Privacy means the service provider can’t read your messages.
- Sovereignty means no government can force that provider to hand over your metadata or shut down your account based on foreign laws.
In 2026, we are seeing the rise of the Sovereign Stack—a collection of tools (like Proton, Nextcloud, and Ollama) that prioritize both privacy and physical control.
How to Achieve Personal Data Sovereignty
If you want to ensure your data is truly yours, follow these four steps:
- Audit Your Storage: Identify where your most sensitive files (photos, tax docs, passwords) are physically stored.
- Choose Local-First Tools: Use applications that store data on your device first, only syncing to the cloud if you choose.
- Self-Host Critical Services: Run your own home server (using tools like Raspberry Pi or old laptops) for backups and media.
- Use Sovereign Jurisdictions: When using cloud services, pick providers based in countries with strong sovereignty protections (e.g., Switzerland, Iceland).
Frequently Asked Questions (FAQ)
What is the difference between data sovereignty and data residency?
Data residency refers to the physical location where data is stored (e.g., a server in Mumbai), while data sovereignty refers to the legal jurisdiction and laws that apply to that data because of its physical location. In 2026, you can have residency in India but if the provider is a US company, you may lack true sovereignty due to the CLOUD Act.
Why does data sovereignty matter for AI development?
AI models are trained on massive datasets. If that data is stored in a jurisdiction with weak sovereignty laws, your intellectual property or personal user data could be subject to foreign government seizure or surveillance without your consent. Sovereign AI requires both local data storage and local model execution.
How does the US CLOUD Act affect global data sovereignty?
The US CLOUD Act allows US law enforcement to subpoena data held by US-based companies, even if that data is physically stored on servers outside the United States. This creates a direct conflict with local laws like the EU’s GDPR or India’s DPDP Act, effectively bypassing local sovereignty protections.
Can I achieve data sovereignty using public cloud providers?
It is difficult but possible using “Sovereign Cloud” offerings from providers like AWS, Azure, or Google, which use dedicated local infrastructure and legal entites. However, the most robust form of data sovereignty is achieved through self-hosting or using local-first, open-source tools where you own the physical hardware and encryption keys.
Is data localisation the same as data sovereignty?
No. Data localisation is a requirement that data stay within a country’s borders. Data sovereignty is the broader legal principle that the data is subject to that country’s laws. You can have localisation without sovereignty if the laws of that country allow foreign access, or if the provider is subject to extra-territorial laws.
Conclusion: The Future is Sovereign
As AI agents begin to manage more of our daily lives, the importance of data sovereignty will only grow. An AI that knows your schedule, your finances, and your health data must be a sovereign AI—one that answers to you, and only you.
By understanding data sovereignty today, you are preparing for a future where digital independence is the only way to guarantee true freedom.
Last Verified: 2026-03-23 | Author: Vucense Editorial Team