The Architecture of Silence: How to build a data-secure digital life

Key Takeaways
- The 'Architecture of Silence' is a design philosophy that prioritizes local-first, encrypted, and minimal digital footprints.
- In 2026, the goal is to reduce 'Digital Noise'—the unnecessary data collection and notifications of modern life.
- Sovereign tech provides the 'Walls' for your digital life, protecting you from surveillance and ad-targeting.
- Silence is not about absence, but about the intentional control of your digital presence.
The Noise of 2026
We live in a world of constant digital noise. From the endless stream of notifications to the silent, invisible trackers that follow us from site to site, our digital lives are loud, cluttered, and exposed.
In 2026, the most valuable luxury is Silence.
Silence is not just the absence of sound; it’s the absence of surveillance. It’s the ability to exist in a digital space that is entirely your own, where your data is not being harvested and your attention is not being sold.
Welcome to the Architecture of Silence.
Pillar 1: Local-First Everything
The foundation of the architecture is Local-First. In the 2010s, we were told the “Cloud” was the future. In 2026, we’ve realized the cloud is just someone else’s server.
A silent digital life begins with local hardware. Your notes, your tasks, your photos, and your code should all live on your device first. The cloud should only be used as an encrypted backup, not as the primary home for your data.
The Sovereign Rule: “If it’s not local, it’s not yours.”
Pillar 2: Encrypted Communication
In a silent architecture, your messages are your own. This means using End-to-End Encryption (E2EE) for everything.
In 2026, E2EE is no longer a “niche” feature. It’s the standard. From Signal for messaging to Proton for email, the goal is to ensure that even the service provider cannot read your data. This is the digital equivalent of a soundproof room.
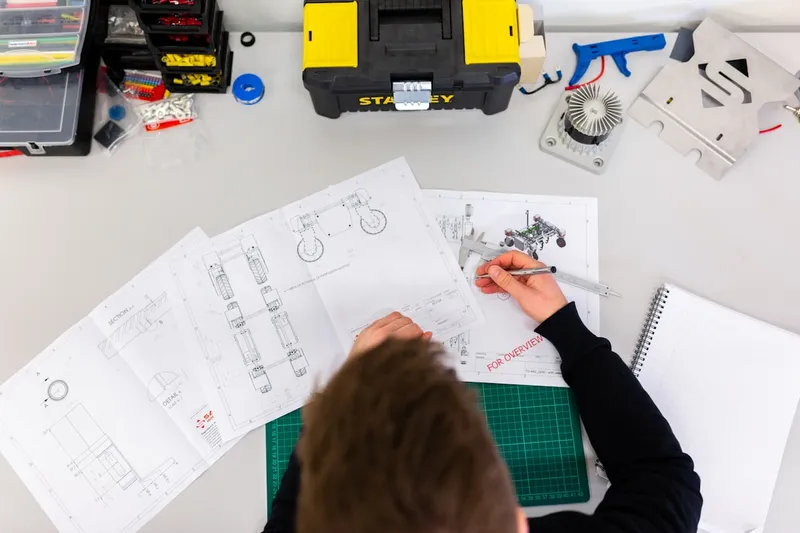
Pillar 3: Minimalist Digital Footprint
The loudest digital lives are the ones with the most accounts. Each account is a new “Leak” in your privacy.
The Architecture of Silence advocates for a Minimalist Digital Footprint.
- Audit Your Accounts: If you haven’t used an account in 6 months, delete it.
- Use “Burner” Emails: Use services like SimpleLogin or Firefox Relay to create unique aliases for every service. This prevents companies from linking your identity across the web.
- Opt-Out by Default: If a service asks for your location, your contacts, or your health data, say “No” unless it’s absolutely essential.
Pillar 4: Sovereign Hardware
The final pillar is the hardware itself. Standard laptops and phones are designed to be “Loud.” They are built to collect telemetry and send it back to the manufacturer.
In 2026, the silent professional chooses Sovereign Hardware.
- Framework Laptops: Modular and open-source, allowing you to control every component.
- System76: Laptops that ship with open-source firmware and no “Backdoors.”
- GrapheneOS: A mobile operating system designed for the ultimate in privacy and silence.
Conclusion: Reclaiming Your Attention
The Architecture of Silence is not about hiding from the world. It’s about reclaiming your attention, your privacy, and your sovereignty. By building a digital life that is quiet by design, you are creating a space where you can truly focus, create, and exist on your own terms.
In 2026, the most powerful thing you can be is Silent.
Vucense is your source for the latest in digital independence and sovereign tech. Subscribe for more.
Comments
Similar Articles
De-Googling Your Life: A 7-day guide to digital independence
Is it possible to live without Google in 2026? Discover the step-by-step process to reclaiming your data and achieving true digital sovereignty.
Confidential Computing: How hardware-level privacy is changing the US tech landscape
In 2026, software encryption is no longer enough. Discover how Confidential Computing is protecting data even while it's being processed.
Setting up a Private Home Server: Your guide to 100% data control
In 2026, the 'Cloud' is someone else's computer. Discover how to build your own private home server and achieve true data sovereignty.