Dirty Frag: When Your Linux System’s Own Kernel Becomes an Attack Vector
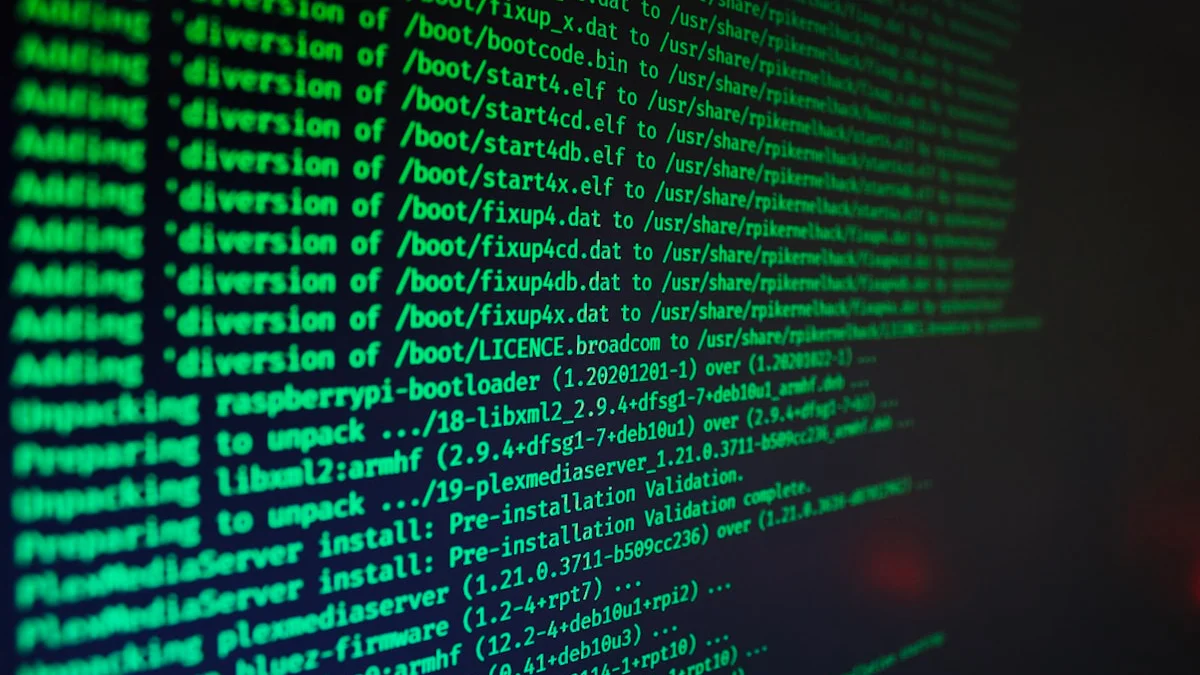
On May 8, 2026, Microsoft’s Defender Security Research Team published an alarming alert: a new Linux privilege escalation vulnerability—codenamed “Dirty Frag”—is actively being exploited by threat actors in the wild.
Dirty Frag (CVE-2026-43284 and CVE-2026-43500) represents one of the most serious Linux kernel vulnerabilities in years. It affects core operating systems—Ubuntu, RHEL, CentOS, Fedora, openSUSE—and it’s already being exploited in real attacks. What makes it particularly dangerous is that it enables reliable privilege escalation from unprivileged user to root, giving attackers complete control of your system.
The name is deceptive. “Dirty Frag” sounds almost whimsical. But what it represents is serious: an attacker with limited local access can escalate to root control of your Linux system, gaining the ability to:
- Disable security monitoring
- Access encrypted credentials
- Tamper with logs and audit trails
- Pivot laterally to other systems
- Establish persistent backdoors
For anyone running self-hosted infrastructure, sovereign systems, or home servers—this vulnerability represents an existential threat to the security model.
And attackers are already using it.
The Vulnerability: Technical Breakdown
Dirty Frag is a Linux kernel local privilege escalation (LPE) vulnerability in how the kernel handles three specific components: esp4 and esp6 (Encapsulating Security Payload for IPsec/VPN), the xfrm subsystem (which handles cross-realm encryption), and the rxrpc module (used in distributed file systems like AFS).
What makes it dangerous isn’t any single piece of code. It’s how the kernel manages memory when these modules operate. Similar to the CopyFail vulnerability (CVE-2026-31431) from earlier this year, Dirty Frag abuses memory fragmentation in the page cache. An attacker can craft specific packet sequences or system calls that force memory corruption. Then, through that corruption, they escalate from unprivileged user to root.
The real danger: it works reliably. Most privilege escalation vulnerabilities depend on race conditions or precise timing windows. They fail half the time. Dirty Frag provides multiple stable attack paths. Hit one wrong? Try the other. This consistency is what makes it particularly lethal in the wild.
Why This Matters: The Linux Privilege Escalation Attack Chain
The Attacker’s Workflow
Most cyberattacks follow a sequential progression:
-
Initial Access: Get a foothold on the target system
- Compromised SSH credentials
- Vulnerable web application
- Container escape
- Phishing → compromised account
- Social engineering
-
Persistence & Privilege Escalation: Establish control
- If you get in as a regular user, escalate to root
- Install backdoors and persistent access
-
Post-Compromise Activities: Expand control
- Access sensitive data
- Compromise other systems
- Establish command and control
Dirty Frag enables step 2 reliably. Once an attacker has any local access, they can escalate to root and own the system completely.
Real-World Example: The Observed Attack
Microsoft Defender documented actual Dirty Frag exploitation happening right now. Here’s the timeline from a real attack:
1. Attacker gains SSH access (credential compromise or successful brute-force)
2. Spawns interactive shell
3. Stages an ELF binary (./update) - the exploit code
4. Executes exploit → immediate privilege escalation via 'su'
5. Now running as root, attacker:
- Modifies GLPI authentication files (changing LDAP config)
- Searches for session files and credentials
- Deletes PHP session files (disrupting active sessions)
- Reads remaining session data (stealing active user credentials)This attack happened in the wild. It wasn’t theoretical. And it succeeded because once SSH access was compromised, Dirty Frag gave the attacker everything else.
Affected Systems: Which Linux Distributions Are Vulnerable to Dirty Frag?
Affected Linux Distributions
- Ubuntu (any version with vulnerable kernel)
- RHEL (Red Hat Enterprise Linux)
- CentOS Stream
- AlmaLinux
- Fedora
- openSUSE
- OpenShift (containerized deployments)
Essentially: if you’re running Linux with IPsec or RxRPC support enabled, you’re potentially vulnerable.
Attack Prerequisites
The exploit requires:
- Local code execution as unprivileged user
- Vulnerable kernel modules loaded (esp4, esp6, or rxrpc)
- Ability to trigger kernel functions (typically through socket operations or system calls)
In other words: you don’t need to be root to exploit this. You just need to be able to run commands on the system.
Common Entry Points
Attackers might gain initial access through:
-
SSH Compromise
- Weak password
- Credential reuse from breached services
- Unauthorized key installation
-
Web Application Vulnerability
- RCE in web app (CMS, forum, admin tool)
- Web shell left by previous attacker
- Vulnerable plugin or dependency
-
Container Escape
- Docker/Kubernetes escape
- Runaway container with privileged options
- Shared kernel vulnerability
-
Service Account Compromise
- Database user with shell access
- Application service account abused
- CI/CD credentials leaked
-
SSH Key Access
- Compromised backup systems
- Shared development keys
- Git repos with embedded keys
The Detection Problem: Why Defenders Miss This
Signature-Based Detection Fails
Traditional security:
- Monitors for known malware signatures
- Looks for specific file changes
- Checks for standard backdoor indicators
Dirty Frag?
- It’s a kernel memory corruption technique
- No distinctive “signature”
- The exploit binary can be compiled differently each time
- The attack leaves minimal forensic evidence
The Staging Timeline
Real attacks show a pattern:
SSH login (flagged as normal login)
↓
Execute ./update binary (undetected - unknown binary)
↓
Privilege escalation (might register as 'su' command, normal on Linux)
↓
Attacker now root (no alert - they belong at root level after escalation)
↓
Modify configuration files (could appear as routine admin activity)
↓
Delete session files (could appear as log rotation)Each individual action looks legitimate. The pattern is malicious.
Why This Is Hard to Defend Against
- Legitimate Usage: IPsec and RxRPC have valid uses
- Low-Level Exploitation: Happens in kernel space, difficult to audit
- No Persistent Artifact: Doesn’t need to install a file-based backdoor
- Rapid Exploitation: From shell access to root in seconds
- Post-Compromise Control: Once root, attacker can disable monitoring
Microsoft Defender’s Active Monitoring
Microsoft has identified several indicators of compromise related to Dirty Frag:
Detected Attack Patterns
| Tactic | Behavior | Detection |
|---|---|---|
| Execution | ELF exploit binary launch | Exploit:Linux/DirtyFrag.A, B |
| Privilege Escalation | Suspicious SUID/SGID process | Microsoft Defender for Endpoint |
| Defense Evasion | Session file deletion | Behavioral monitoring |
| Credential Theft | Accessing PHP session files | Log analysis |
| Impact | GLPI/LDAP config modification | System integrity checking |
Coverage Available
- Microsoft Defender Antivirus: Detects exploit binaries
- Microsoft Defender for Endpoint: Monitors suspicious privilege escalation
- Microsoft Defender for Cloud: Alerts on detected dirtyfrag exploitation
- Vulnerability Management: Identifies systems vulnerable to CVE-2026-43284
Mitigation: Protecting Your Linux Systems
Immediate Actions (This Week)
1. Kernel Patching
Status as of May 8, 2026:
- CVE-2026-43284 patch released by Linux Kernel Organization
- CVE-2026-43500 patch still pending (not yet in NVD)
Action:
# For Ubuntu/Debian
sudo apt update
sudo apt full-upgrade
# For RHEL/CentOS
sudo yum update kernel
# Reboot to activate new kernel
sudo rebootCheck kernel version:
uname -rTimeline: Apply patches immediately if available for your distribution.
2. Disable Unused Kernel Modules
If you don’t actively use IPsec VPN or RxRPC, disable the vulnerable modules:
# Create modprobe config to prevent vulnerable modules from loading
sudo tee /etc/modprobe.d/disable-dirtyfrag.conf << EOF
install esp4 /bin/false
install esp6 /bin/false
install rxrpc /bin/false
EOF
# Unload active modules (if safe for your workload)
sudo modprobe -r esp4 2>/dev/null
sudo modprobe -r esp6 2>/dev/null
sudo modprobe -r rxrpc 2>/dev/nullWarning: Only do this if you’re certain your system doesn’t use:
- IPsec VPN connections
- VPN software that requires xfrm/esp modules
- Distributed file systems that rely on RxRPC
Short-Term Defenses (Next 2 Weeks)
3. Harden Local Access
Since Dirty Frag requires initial local access, make initial access harder:
SSH Hardening:
# Disable password auth, use keys only
sudo nano /etc/ssh/sshd_config
# Set these options:
PasswordAuthentication no
PubkeyAuthentication yes
PermitRootLogin no
PermitEmptyPasswords no
# Restrict to specific users
AllowUsers username
# Restart SSH
sudo systemctl restart sshdFail2Ban (Rate Limiting):
sudo apt install fail2ban
sudo systemctl enable fail2ban
sudo systemctl start fail2banKey-Based SSH Only:
- Generate strong SSH keys (4096-bit RSA or ed25519)
- Distribute public keys only
- Rotate keys regularly
4. User Access Review
List all accounts on your system:
cut -d: -f1 /etc/passwd | grep -v rootRemove unnecessary accounts. Each account is a potential attack surface.
5. Web Application Security
If running web applications:
- Keep CMS and plugins updated
- Use Web Application Firewalls (ModSecurity)
- Regular security scanning
- Remove unused plugins/features
6. Container Security (If Using Docker/Kubernetes)
# Don't run containers with --privileged
docker run --security-opt=no-new-privileges ...
# Use AppArmor/SELinux profiles
# Implement network policies
# Regular image scanningMedium-Term Strategies (Ongoing)
7. Post-Compromise Integrity Verification
Even if you patch, verify your system wasn’t compromised before:
Check for rootkits/backdoors:
# Install rootkit detection
sudo apt install chkrootkit rkhunter
# Run detection
sudo chkrootkit
sudo rkhunter --check --skip-keypressClear kernel page cache (if suspicious):
# Warning: impacts I/O performance temporarily
echo 3 | sudo tee /proc/sys/vm/drop_caches
# Then verify file integrity
aide --check # If you're using AIDECheck for suspicious accounts/permissions:
# Look for accounts with UID 0 (root)
awk -F: '($3 == 0) {print}' /etc/passwd
# Check for setuid binaries (uncommon ones are red flags)
find / -perm -4000 -ls 2>/dev/null | grep -v expected_binaries8. Intrusion Detection & Monitoring
Implement behavior-based monitoring:
Option A: OSSEC (Open Source HIDS)
sudo apt install ossec-hids
# Monitors file changes, logs, process behaviorOption B: Auditd (Linux Audit Framework)
sudo apt install auditd
# Monitor privilege escalation attempts
sudo auditctl -w /etc/sudoers -p wa -k sudoers_changesOption C: Wazuh (Enterprise-grade HIDS)
- Open source, distributed monitoring
- Detects suspicious process behavior
- Correlates events
9. Firewall & Network Segmentation
# UFW (Ubuntu Firewall)
sudo ufw enable
sudo ufw default deny incoming
sudo ufw default allow outgoing
sudo ufw allow 22/tcp # SSH only
sudo ufw allow 80/tcp # HTTP if needed
sudo ufw allow 443/tcp # HTTPS if neededFor home servers, consider:
- VPN-only access (WireGuard/OpenVPN)
- Port knocking
- Network segmentation (separate VLANs)
The Broader Context: Privilege Escalation Vulnerabilities Are Multiplying
Dirty Frag isn’t an anomaly. It’s part of a pattern:
Recent Linux LPE Vulnerabilities:
- CopyFail (CVE-2026-31431): Similar memory corruption technique
- Dirty Pipe (CVE-2022-0847): Prior memory corruption exploit
- PwnKit (CVE-2021-4034): PKexec vulnerability
- Polkit Issues: Multiple privilege escalation paths
The Trend: As the Linux kernel grows more complex, finding privilege escalation paths becomes easier for sophisticated attackers.
The Implication: You can’t rely on “just using Linux” for security. You need defense-in-depth:
- Minimize local access paths
- Keep systems patched
- Monitor behavior
- Implement least-privilege access
- Segment networks
Sovereignty Implications: Why This Matters for Self-Hosted Systems
If you’re running a sovereign stack—self-hosting your email, files, search, or other critical services—Dirty Frag threatens the entire security model.
The Self-Hosting Risk Model
Your Home Server
↓
Your Data (email, files, configs)
↓
Your Credentials (API keys, passwords)
↓
Your Network (what can the compromised server access?)If an attacker gets shell access and escalates to root:
- Access all your data (no file permissions restrict root)
- Steal all credentials (root can read /home, /root, encrypted vaults)
- Compromise your entire network (root can configure firewall, DNS, routing)
- Establish persistence (cron jobs, systemd timers, kernel modules)
The privilege escalation vulnerability collapses your entire security perimeter.
Defense-in-Depth for Sovereignty
-
Zero-Trust Local Access
- Assume shell access will happen
- Encrypt sensitive data with keys not stored on system
- Use dedicated hardware security modules if possible
-
Immutable Infrastructure
- Use read-only root filesystem where possible
- Separate configuration from state
- Version control system state
-
Compartmentalization
- Different services on different systems
- VPN between internal systems
- Firewall between data storage and application services
-
Continuous Monitoring
- Regular log review
- Unexpected process alerting
- Network traffic analysis
Patching Timeline & Vendor Updates
Available Now (May 8+)
- CVE-2026-43284: Patches available
- Linux Kernel: Updated in:
- Ubuntu 24.04 LTS (Canonical priority)
- RHEL 9.x
- CentOS Stream
Pending
- CVE-2026-43500: Patch development ongoing
- Older kernel versions: May not receive patches (end-of-life consideration)
Checking Your System Status
# Check if you're on vulnerable kernel
uname -r
# Check which vulnerabilities your kernel might be susceptible to
# (requires specific tools or kernel symbols)
# Check if vulnerable modules are loaded
lsmod | grep -E 'esp4|esp6|rxrpc'What Organizations Are Doing
Microsoft’s Response
- Active monitoring for exploitation attempts
- Threat analytics articles published
- Detection signatures deployed to Defender customers
- Posture guidance in development
Linux Kernel Community
- CVE-2026-43284 patched (May 8)
- CVE-2026-43500 investigation ongoing
- Stable releases being updated progressively
- LTS kernels prioritized for patches
Enterprise Security
- Mandatory kernel patching
- Disable vulnerable modules policy
- Privilege escalation monitoring
- Incident response plans updated
The Bottom Line: Act Now, Not Later
Dirty Frag represents a high-severity, actively exploited vulnerability in a fundamental Linux subsystem.
The good news: patches are available, mitigations are straightforward.
The bad news: every day of delay increases risk.
If you’re running:
- A home server
- Self-hosted infrastructure
- Any Linux system accessible to users or over the network
Your action items:
- This week: Apply kernel patches
- This week: Disable unused IPsec/RxRPC modules
- This week: Harden SSH (keys only, no passwords)
- This month: Implement intrusion detection
- Ongoing: Monitor for suspicious activity
The privilege escalation vulnerability collapses in 1-2 minutes once initial access is established. Your defense is preventing that initial access and detecting the post-compromise activities quickly.
This vulnerability isn’t “another CVE to track.” It’s an active threat in the wild, being exploited against real systems right now.
Treat it accordingly.
Frequently Asked Questions: Dirty Frag Linux Vulnerability
Q1: What exactly does “privilege escalation” mean in the context of Linux security?
Privilege escalation is when an attacker goes from a limited account (unprivileged user) to a powerful account (root/administrator). On Linux:
- Unprivileged user can read their own files, run their own programs
- Root can read ANY file, modify ANY system setting, disable security monitoring, install backdoors
Privilege escalation is the attacker’s goal because it transforms limited access into complete system control.
Q2: Why is Dirty Frag different from other Linux privilege escalation vulnerabilities?
Most LPE vulnerabilities rely on race conditions or narrow timing windows:
- Attacker must exploit at exactly the right microsecond
- Reliability is often 50-70%
- Requires multiple attempts
Dirty Frag provides multiple stable attack paths (esp4, esp6, rxrpc) that:
- Don’t depend on precise timing
- Work reliably across different kernel versions
- Can succeed on first attempt
- More difficult to defend against
This is why it’s particularly dangerous.
Q3: What distributions are affected?
Confirmed vulnerable:
- Ubuntu (all currently supported versions)
- Red Hat Enterprise Linux (RHEL)
- CentOS Stream
- AlmaLinux
- Fedora
- openSUSE
- OpenShift (Kubernetes)
Essentially: any Linux distribution with vulnerable kernel modules loaded.
Q4: Do I need IPsec/RxRPC for the vulnerability to affect me?
For basic users: Probably not actively using it, but the modules might be loaded by default.
For businesses/home servers: Possibly—if you run VPN software or distributed file systems.
Check if vulnerable:
lsmod | grep -E 'esp4|esp6|rxrpc'If output is empty, these modules aren’t loaded. If they show up, they’re loaded and potentially vulnerable.
Q5: Can I protect my Linux system against Dirty Frag if I can’t patch the kernel yet?
Short-term mitigations (while waiting for patches):
-
Disable modules (if safe for your workload):
sudo modprobe -r esp4 esp6 rxrpc -
Harden SSH (prevent initial access):
- Disable password authentication
- Use SSH keys only
- Restrict to specific users
- Run on non-standard port
-
Monitor for privilege escalation:
- Use auditd to track
sucommands - Alert on unexpected SUID process launches
- Monitor /etc/sudoers changes
- Use auditd to track
-
Segment network:
- Isolated VLAN for critical systems
- Firewall rules restricting local access
-
Regular backups:
- If exploited, you can recover
- Store backups offline
These don’t fix the vulnerability, but they make exploitation harder.
Q6: What’s the difference between CVE-2026-43284 and CVE-2026-43500?
| CVE | Component | Status | Impact |
|---|---|---|---|
| CVE-2026-43284 | esp4, esp6 (IPsec) | Patch released May 8 | High - widely used |
| CVE-2026-43500 | rxrpc | Patch pending | Medium - less common |
Both are Dirty Frag, both allow privilege escalation, but they exploit different kernel components.
Q7: How does the attack actually happen? (Technical)
Simplified flow:
- Attacker gains initial shell (SSH compromise, web shell, etc.)
- Attacker triggers kernel memory corruption via crafted IPsec/RxRPC packets
- Kernel memory fragmentation creates exploitable state
- Attacker escalates to root via memory corruption
- Root access achieved - attacker now owns system
The vulnerability is in steps 2-4—the memory handling in the kernel.
Q8: What does “memory fragmentation” mean?
Think of system memory as a bookshelf:
- Each program gets shelf space
- When programs finish, space gets freed
- New programs use the freed space
“Memory fragmentation” is when freed space gets split into small, scattered pieces. Dirty Frag exploits the kernel’s process of managing this fragmentation to cause corruption that can be escalated to root access.
Q9: Is container/Docker escape possible via Dirty Frag?
Yes. If:
- Attacker escapes the container (separate vulnerability)
- Container runs on vulnerable kernel
- Attacker exploits Dirty Frag to escalate to host root
This is particularly dangerous because containerization provides zero isolation against kernel vulnerabilities. Patching the host kernel is critical.
Q10: What should I do if I suspect my system was compromised?
Immediate actions:
-
Isolate the system - disconnect from network if possible
-
Check for indicators of compromise:
# Check for unexpected root processes ps aux | grep root # Check recently modified files find / -mtime -1 -type f 2>/dev/null # Check for backdoor accounts grep ':0:' /etc/passwd # Check cron jobs crontab -l -
Review logs:
sudo journalctl -u sshd | tail -100 sudo tail -100 /var/log/auth.log -
If compromise confirmed:
- Assume all credentials are compromised
- Wipe and rebuild from trusted backup
- Change all passwords from different computer
- Review network activity from the affected system
- Contact security if you handle sensitive data
Q11: Why is rootkit detection important?
Once attacker has root, they can:
- Install kernel-level rootkits
- Hide malicious processes and files
- Intercept system calls
- Modify logs to cover tracks
Rootkit detection (chkrootkit, rkhunter) can catch some malicious modifications, but sophisticated rootkits can evade detection. Prevention (patching quickly) is better than detection (finding rootkit afterward).
Q12: How does this affect Kubernetes / container orchestration?
Direct risk:
- Attacker compromises container
- Exploits kernel vulnerability on host
- Escapes to host root
- Compromises entire cluster
Protection strategy:
- Patch host kernels immediately
- Use gVisor (user-space kernel proxy) for additional container isolation
- Network policies restricting container communication
- Pod security standards limiting container capabilities
- Regular cluster security audits
Container security is only as good as the underlying kernel security.
Q13: What’s the timeline for patches across different distributions?
As of May 12, 2026:
| Distribution | CVE-2026-43284 Status | CVE-2026-43500 Status |
|---|---|---|
| Ubuntu | Patch available | Patch available |
| RHEL 9 | Patch available | Patch available |
| CentOS Stream | Patch available | Patch available |
| Fedora | Patch available | Patch available |
| AlmaLinux | Patch available | Patch available |
| openSUSE | Patch available | Patch available |
| Older kernels | May not be patched (end-of-life) | May not be patched |
Check your specific version:
uname -r
# Then check distribution security advisory for your versionQ14: What about home server security best practices beyond Dirty Frag?
A comprehensive home server defense includes:
- Patching discipline - monthly minimum
- Access hardening - SSH keys, strong auth
- Network segmentation - separate VLANs for services
- Monitoring - intrusion detection, behavior monitoring
- Backups - regular offline backups
- Encryption - data at rest, data in transit
- Principle of least privilege - minimize service account permissions
- Regular audits - vulnerability scans, permission reviews
Dirty Frag is just one of many threats. A layered approach is essential.
Q15: Is privilege escalation the only way attackers exploit Dirty Frag?
Yes, privilege escalation is the core exploitation goal. But the impact varies:
- Attacker with shell as
www-data(web server) → escalates to root → owns web server + underlying data - Attacker with SSH as regular user → escalates to root → owns entire server + can pivot to network
- Container escape → Dirty Frag escalation → owns container host + potentially entire cluster
The exploit path is the same (memory corruption → root), but the initial access vector varies.
Q16: How common will memory-based kernel exploits become?
Memory corruption vulnerabilities are increasing, not decreasing, because:
- Complex kernel code - IPsec, RxRPC, and similar subsystems have massive codebases
- Hardware aging - Older systems have accumulated kernel patches and edge cases
- AI-assisted discovery - Just like with zero-days, AI can find memory bugs at scale
- Fragmentation exploitation - Dirty Frag’s technique (exploiting memory fragmentation) is replicable across many subsystems
Forecast (2026-2027):
- Expect 3-5 major kernel privilege escalation vulnerabilities per year
- Some will get patches in days, others will take weeks
- Older distributions (outside vendor support) will become increasingly vulnerable
- This is why constant patching becomes a security baseline, not optional
Q17: What should enterprise/organizational security teams do immediately?
Actionable steps for IT/Security leadership:
-
Inventory all Linux systems (servers, desktops, containers, IoT)
- Identify supported vs. unsupported distributions
- Flag systems beyond vendor support windows
-
Patch management acceleration
- Move from quarterly to monthly patching for kernel security
- Automate where possible
- Accept short downtime for critical patches
-
Monitoring deployment
- Deploy auditd or EDR tools monitoring privilege escalation attempts
- Alert on
sucommands, SUID binary execution, sudoers modifications - Monitor for privilege escalation patterns (memory spikes, unusual system calls)
-
Network segmentation
- Isolate legacy/unpatched systems from critical infrastructure
- Restrict local access networks
- Implement zero-trust architecture for internal networks
-
Incident response readiness
- Assume breach = attacker now has root
- Prepare credential rotation procedures
- Maintain isolated forensics infrastructure
- Document which systems contain sensitive data requiring extra protection
-
Vendor communication
- Contact Linux vendors for patch timelines
- Establish security advisory subscriptions
- Plan infrastructure upgrades for end-of-life systems
Q18: How does Dirty Frag affect self-hosted / sovereign infrastructure?
Dirty Frag directly threatens sovereignty because:
-
Self-hosted = You’re the vendor
- There’s no support team to contact
- Patches must be applied manually by your team
- Delays in patching = vulnerability window
- Missed patches = compromise risk
-
Sovereignty requires security
- Data ownership without infrastructure security is false sovereignty
- Compromised self-hosted systems expose all stored data
- Attacker can modify encrypted data keys, delete backups, install persistent backdoors
- Sovereignty only works if your infrastructure can be defended
-
Practical implications
- Minimal attack surface: Run only essential services, disable kernel modules you don’t need (esp4, esp6, rxrpc)
- Aggressive patching: Self-hosted systems should patch within 48 hours of vendor release
- Defense-in-depth: Can’t rely on perimeter—harden every layer
- Offline backups: If compromised, you can recover. Online backups = attacker can delete them
- Monitoring focus: Self-hosted systems need more aggressive behavioral monitoring than cloud infrastructure
-
Sovereignty scoring impact
- Unpatched self-hosted system: Sovereignty score = 0 (compromisable)
- Patched but unmonitored: Sovereignty score = 40-50 (vulnerability window risk)
- Patched + hardened + monitored: Sovereignty score = 80+ (practical defense)
Sovereignty is a security responsibility, not just a philosophical choice. Dirty Frag is a reminder that self-hosting requires active security maintenance.
Related Security Articles & Resources
Immediate Linux Security:
- How to Audit Your App Permissions on iOS and Android — Apply permission hardening principles to your systems
- How to Encrypt Your Entire Digital Life: The Complete Guide — Prepare for post-compromise data protection
- How to Block All Ads and Trackers on Your Home Network — Network segmentation as intrusion defense
Regulatory & Governance Context:
- UK AI Safety Institute 2026: Statutory Rulings on Data Sovereignty — How regulations mandate security practices for infrastructure
- Anthropic vs Pentagon: The AI Safety Lawsuit of 2026 — Legal frameworks around critical infrastructure protection
Sovereign Infrastructure:
- Sovereign Multi-Agent Orchestration: Building Trustworthy AI Systems — Automated defense strategies for self-hosted systems
- Claude Code Auto Mode Review 2026 — Using AI safely in your infrastructure code
Privacy & Device Security:
- Best Privacy Phones 2026: Security Comparison — Securing your mobile access points to infrastructure